Windows Defender in Windows 11 behaves Malware-Like…
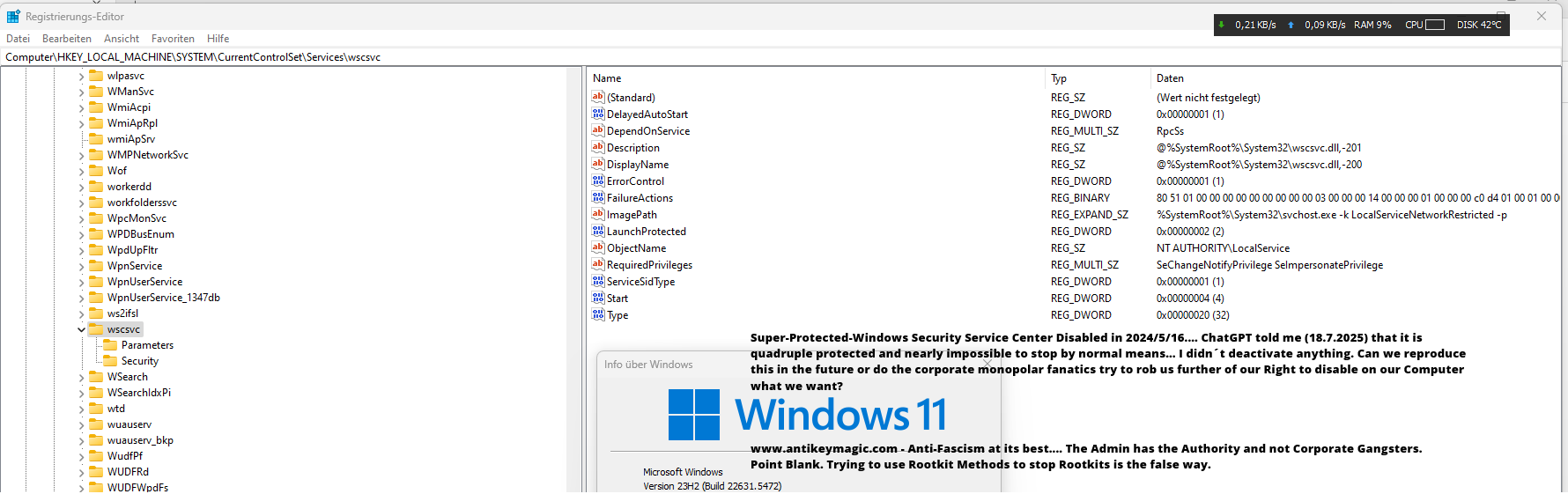
It forces itself automatically over the free will of the user which is Malware-Like, it bypasses your decision to shut it down, which is Malware-Identical. It uses Shadow Table Hooks to prevent the Administrator from stopping it, which is Malware-Identical. It attacks 3rd Party Security Tools to stop them from finding their Malware-Tactics which is Malware-Like. It automatically reactivates itself against the Will of the Administrator which is Malware-Identical and Totalitarian. The Admin ought to have full decision control over his Operation System, we are experienced enough to take full control over our systems.
//
Der Windows Defender in Windows 11 verhält sich Malware-ähnlich…
Er drängt sich automatisch über den freien Willen des Benutzers, was Malware-ähnlich ist, er umgeht deine Entscheidung, ihn abzuschalten, was Malware-identisch ist. Er verwendet Schattentabellenhaken, um zu verhindern, dass der Administrator ihn stoppen kann, was Malware-identisch ist. Er greift Sicherheitstools von Drittanbietern an, um sie daran zu hindern, seine Malware-Taktiken zu finden, was Malware-ähnlich ist. Er reaktiviert sich automatisch gegen den Willen des Administrators, was mit Malware identisch und totalitär ist. Der Administrator sollte die volle Entscheidungskontrolle über sein Betriebssystem haben. Wir sind erfahren genug, um die volle Kontrolle über unsere Systeme zu übernehmen.
Okay Windows Defender, Game Over, Power Battle Won… I am the Admin, not You.
/
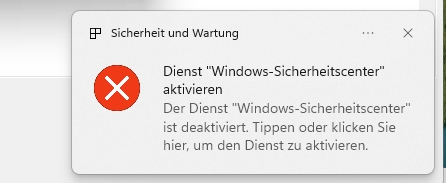
To remove the Shadow Table Hooks of WinDefender to change zw set value, you need a special registry Software.
//
Okay, Windows Defender, das Spiel ist aus, Machtkampf gewonnen … Ich bin der Admin, nicht du.
/
Um die Schattentabellenhaken von WinDefender zu entfernen und den ZW-Setz-Wert zu ändern, benötigst du eine spezielle Registry Software.
AVZ below v. 5.x is the only Anti-Rootkit left that finds the Shadow Table Hooks of Windows Defender? Devolution….where are all the legendary enthusiastic little software tools from 2005 to 2019….
Windows Defender uses Rootkit Techniques… silly to the core…Just find a good Unhooker, which is rare these days…
Windows Defender can be deactivated, I nearly forgot the oldschool way…. safe boot remove autostart windefend.
//
Windows Defender lässt sich deaktivieren, fast hätte ich die Oldschool/Altmodische-Methode vergessen…. Windows im abgesicherten Modus starten und den Windefend-Autostart entfernen.
Local Security Authority of Windows 11 attacks Oshi Unhooker and shuts it down… to prevent the unveiling of their SSDT Hooks… This is malware-like behavior of Windows 11.
//
Die lokale Sicherheitsauthorität von Windows 11 greift Oshi Unhooker an und schaltet ihn ab… um die Enthüllung ihrer SSDT-Hooks zu verhindern … Dies ist ein Malware-ähnliches Verhalten von Windows 11.
AVZ 4.46 Proves the Hooks:
Scanning started at 16.05.2024
Heuristic microprograms loaded: 412
AVZ is run with administrator rights (+)
1. Searching for Rootkits and other software intercepting API functions
1.1 Searching for user-mode API hooks
Analysis: kernel32.dll, export table found in section .rdata
Function kernel32.dll:ReadConsoleInputExA (1163) intercepted, method – ProcAddressHijack.GetProcAddress ->76C1F421->75E38A50
Function kernel32.dll:ReadConsoleInputExW (1164) intercepted, method – ProcAddressHijack.GetProcAddress ->76C1F454->75E38A80
Analysis: ntdll.dll, export table found in section .text
Function ntdll.dll:NtCreateFile (301) intercepted, method – ProcAddressHijack.GetProcAddress ->77A66D60->70065210
Function ntdll.dll:NtSetInformationFile (613) intercepted, method – ProcAddressHijack.GetProcAddress ->77A66A80->70065380
Function ntdll.dll:NtSetValueKey (646) intercepted, method – ProcAddressHijack.GetProcAddress ->77A66E10->700653F0
Function ntdll.dll:ZwCreateFile (1879) intercepted, method – ProcAddressHijack.GetProcAddress ->77A66D60->70065210
Function ntdll.dll:ZwSetInformationFile (2189) intercepted, method – ProcAddressHijack.GetProcAddress ->77A66A80->70065380
Function ntdll.dll:ZwSetValueKey (2222) intercepted, method – ProcAddressHijack.GetProcAddress ->77A66E10->700653F0
Analysis: user32.dll, export table found in section .text
Function user32.dll:CallNextHookEx (1536) intercepted, method – ProcAddressHijack.GetProcAddress ->7785E5D0->700650F0
Function user32.dll:EnumWindows (1774) intercepted, method – ProcAddressHijack.GetProcAddress ->7787D090->70065E30
Function user32.dll:GetWindowThreadProcessId (2011) intercepted, method – ProcAddressHijack.GetProcAddress ->7785E7A0->70065E60
Function user32.dll:IsWindowVisible (2094) intercepted, method – ProcAddressHijack.GetProcAddress ->77854CC0->70065E90
Function user32.dll:MessageBoxA (2148) intercepted, method – ProcAddressHijack.GetProcAddress ->778AB310->70067EC0
Function user32.dll:MessageBoxExA (2149) intercepted, method – ProcAddressHijack.GetProcAddress ->778AB360->70067F20
Function user32.dll:MessageBoxExW (2150) intercepted, method – ProcAddressHijack.GetProcAddress ->778AB390->70067F80
Function user32.dll:MessageBoxIndirectA (2151) intercepted, method – ProcAddressHijack.GetProcAddress ->778AB3C0->70067FE0
Function user32.dll:MessageBoxIndirectW (2152) intercepted, method – ProcAddressHijack.GetProcAddress ->778AB500->70068030
Function user32.dll:MessageBoxW (2155) intercepted, method – ProcAddressHijack.GetProcAddress ->778AB830->70068090
Function user32.dll:SetWindowsHookExW (2400) intercepted, method – ProcAddressHijack.GetProcAddress ->77862C50->70065460
Function user32.dll:ShowWindow (2409) intercepted, method – ProcAddressHijack.GetProcAddress ->77864E80->700680F0
Function user32.dll:Wow64Transition (1504) intercepted, method – CodeHijack (not defined)
Analysis: advapi32.dll, export table found in section .text
Function advapi32.dll:CveEventWrite (1234) intercepted, method – ProcAddressHijack.GetProcAddress ->75889300->75E3C940
Function advapi32.dll:I_ScRegisterPreshutdownRestart (1366) intercepted, method – ProcAddressHijack.GetProcAddress ->7588A084->75AEAE50
 You also could rename the dll by external means (via another os) but this will destroy the ability to start Windows 11…They use aggressive hooking techniques to prevent the average Joe Doe from doing anything against their Digital Dictation that blocks intuitive workflow.
You also could rename the dll by external means (via another os) but this will destroy the ability to start Windows 11…They use aggressive hooking techniques to prevent the average Joe Doe from doing anything against their Digital Dictation that blocks intuitive workflow.